Confidential computing significantly enhances the security of e-commerce transactions and is particularly crucial for humanitarian aid workers operating in sensitive areas. This technology encrypts data both in use and when at rest, offering robust protection against cyber threats. It ensures that financial and personal information remains confidential and secure throughout online transactions, including during data transit via encryption methods like TLS and SSL. For humanitarian aid workers who handle sensitive donor and beneficiary data, the adoption of confidential computing within e-commerce platforms provides a secure environment for processing contributions, ensuring integrity and confidentiality. The technology is also vital for e-commerce buyers, who can engage in secure online shopping knowing their sensitive data is protected. As confidential computing becomes more integral to e-commerce, it underscores its importance in safeguarding online transactions globally, particularly for humanitarian aid workers who rely on the robust security it offers to maintain the trust and privacy of their operations and donors.
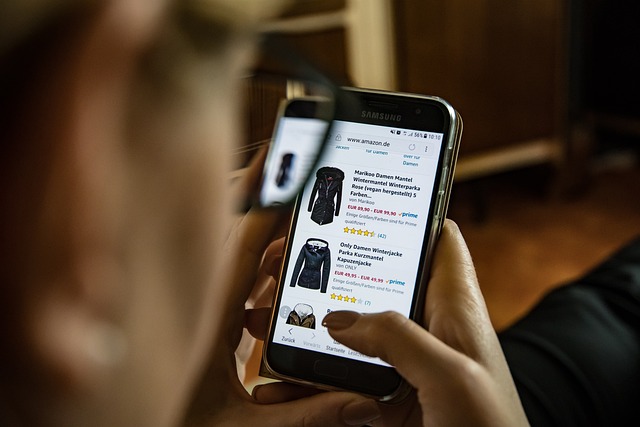
Navigating the digital marketplace, e-commerce buyers are increasingly engaged in online transactions. This article demystifies secure online purchases, highlighting the critical role of confidential computing in safeguarding these exchanges. Delving into best practices for ensuring transaction integrity, we also explore how confidential computing bolsters humanitarian aid workers’ secure online donation processes. Join us to understand the intricacies of e-commerce security and the transformative impact of confidential computing on both commerce and charity.
- Understanding Secure Online Transactions in E-commerce: A Primer for Buyers
- The Role of Confidential Computing in Protecting E-commerce Transactions
- Best Practices for E-commerce Buyers to Ensure Transaction Security
- How Confidential Computing Supports Humanitarian Aid Workers in Secure Online Donations
Understanding Secure Online Transactions in E-commerce: A Primer for Buyers

When engaging in e-commerce, understanding the mechanisms that underpin secure online transactions is paramount for buyers to protect their financial information and maintain trust in digital marketplaces. Confidential computing emerges as a pivotal technology in this context, particularly for humanitarian aid workers who operate in sensitive environments where data protection is critical. This advanced security model ensures that data processed by software and accessed by authorized users remains confidential and unaltered during processing, both in transit and at rest. It achieves this through hardware-based protections that prevent unauthorized users from gaining access to sensitive information, even if the underlying infrastructure is compromised.
For buyers, the assurance of secure online transactions hinges on the adoption of robust encryption methods and the implementation of up-to-date security protocols such as Transport Layer Security (TLS) and Secure Sockets Layer (SSL). These protocols establish a secure connection between the buyer’s device and the e-commerce platform, safeguarding personal and payment details from interception or unauthorized access. Additionally, reputable platforms employ multi-factor authentication (MFA) to add an extra layer of security for account access, ensuring that even if passwords are compromised, transactions remain secure. By understanding these elements and selecting e-commerce sites with a strong commitment to confidential computing, buyers can confidently participate in the digital marketplace, knowing their sensitive data is protected throughout the transaction process.
The Role of Confidential Computing in Protecting E-commerce Transactions
Confidential computing emerges as a pivotal technological advancement in safeguarding e-commerce transactions, particularly for humanitarian aid workers who operate within sensitive environments. This security model ensures that data processed by applications is kept confidential and protected from potentially malicious actors, even as it is processed. By encrypting data both in use and at rest, confidential computing provides a robust layer of protection against data breaches, which is critical given the financial and personal information exchanged in online commerce. This approach is particularly beneficial for humanitarian aid workers who must handle donor information and beneficiary details with the utmost privacy and security. The integration of confidential computing within e-commerce platforms not only instills trust among users but also enables these workers to process contributions securely, ensuring that the intended recipients receive the support meant for them without compromising their financial integrity or personal data. As e-commerce continues to expand globally, the role of confidential computing in protecting these transactions becomes increasingly vital, offering a secure framework that aligns with the growing demand for privacy and data security in the digital marketplace.
Best Practices for E-commerce Buyers to Ensure Transaction Security

When engaging in online transactions, e-commerce buyers must prioritize security to safeguard their financial and personal information. One of the best practices for ensuring transaction security is to understand the encryption methods used by e-commerce platforms. Confidential computing, a technology that allows data to be processed without exposing it in an unencrypted form, is particularly beneficial for e-commerce. It ensures that sensitive information such as credit card details and personal identifiers are protected throughout the transaction process, from the point of purchase to the moment of payment processing.
E-commerce buyers should also verify the legitimacy of the website they are transacting with by looking for HTTPS in the URL, which indicates a secure connection, and checking for trust seals from recognized payment providers like Visa or MasterCard. Utilizing strong, unique passwords and two-factor authentication (2FA) adds an additional layer of security. Additionally, keeping software and operating systems up to date with the latest security patches is crucial to prevent vulnerabilities that could be exploited by malicious actors. For humanitarian aid workers who operate in sensitive environments, confidential computing can be a game-changer, ensuring the integrity and confidentiality of their transactions, even when working remotely or in areas with less secure network infrastructure. By adhering to these best practices, e-commerce buyers can significantly reduce the risk of security breaches and conduct their online transactions with greater confidence and safety.
How Confidential Computing Supports Humanitarian Aid Workers in Secure Online Donations

Confidential computing emerges as a pivotal technology in safeguarding online donations for humanitarian aid workers. By leveraging this approach, sensitive financial data can be processed and stored on remote servers while ensuring that data remains confidential and protected from unauthorized access or breaches. This is particularly critical for humanitarian organizations where the integrity of the financial contributions is paramount to their operations. Confidential computing provides an additional layer of security by encrypting the data in use, not just at rest or in transit, but throughout all processing stages. This means that when a donor contributes to a cause through an online platform, they can be confident that their personal and financial information is securely handled, even as it traverses the complex ecosystem of the internet. The implications for humanitarian aid workers are profound; they can now accept and process donations without exposing contributors’ sensitive data to potential cyber threats, thereby fostering a more trustworthy and reliable environment for charitable giving. As online transactions become increasingly common, the adoption of confidential computing offers a robust defense against the evolving landscape of cybersecurity challenges, ensuring that humanitarian aid workers can focus on their critical missions rather than the security of their donations.
In conclusion, e-commerce buyers are increasingly empowered to engage in secure online transactions thanks to the advancements in technologies like Confidential Computing. This article has outlined the critical aspects of maintaining transaction security, emphasizing its importance for all users, particularly humanitarian aid workers who rely on these systems for critical donations. By adhering to best practices and understanding the mechanisms behind confidential computing, buyers can confidently participate in the e-commerce ecosystem. As a result, both individual consumers and organizations involved in humanitarian efforts benefit from a safer online environment, facilitating trust and reliability in digital marketplaces worldwide.



